Today, Betsy is speaking with Sajan Gautam, CISO at Arvis Bank. Join us as they discuss leveraging AI for threat detection, establishing customer trust through data security, and the importance of cross team collaboration on cybersecurity awareness. Let’s get started on the RevTech Revolution.
Guest bio: Sajan Gautam is the Chief Information Security Officer (CISO) for Arvest Bank where he is responsible for overseeing and executing Information Security and the Business Continuity Program.
Prior to joining Arvest, Sajan spent 15+ years in various information security roles – primarily within financial sector. He led and managed global teams responsible for: information security strategy; performing risk assessment against industry frameworks, rules and regulations; achieving certifications against established standards, etc. As such, he participated in various inter-institution forums to discuss, evaluate and drive advocacy around Cybersecurity frameworks, rules and regulations.
He has a MBA and CISO – Executive Education and numerous professional certifications such as CISSP, CISM, and CIPP/IT. He has instructed, and guest lectured at universities on Cybersecurity topics as well as served as an advisory board member.
Subscribe and listen to the Rev-Tech Revolution podcast series on:
 |
 |
 |
| Spotify | Apple Podcasts | iHeart Radio |
Prefer reading over listening? We got you covered!
Announcer: Welcome to the RevTech Revolution. Today, Betsy is speaking with Sajan Gautam, CISO at Arvis Bank. Join us as they discuss leveraging AI for threat detection, establishing customer trust through data security, and the importance of cross team collaboration on cybersecurity awareness. Let’s get started on the RevTech Revolution.
Betsy Peters: Hello and welcome. We are thrilled today to have Sajan Gautam join us for the RevTech revolution. Sajan, welcome.
Sajan Gautam: Thank you for having me. Thank you for the opportunity.
Betsy Peters: We are thrilled to have you. One of the things that I think is so impressive about you and will be great for our audience to know about is you’ve spent 20 years developing and implementing information security programs with scopes that span from the local to the global. What got you interested in this work? And did you always know you wanted to be involved with computers and security in particular?
Sajan Gautam: That’s a very great question. I did not know, because initially when I started in computing, it was one interest led to another.
I wanted to fix some of the networking issues, then that led into identity and access management, systems administration, firewall. So on and so forth. Now, I do love it because now I’m also doing their cyber risk management and whole gamut of things.
Betsy Peters: That’s great. Did you have any passions as a child that kind of, in the rearview mirror, it makes sense that you’re doing what you’re doing now?
Or is this just, like you said, one thing led to another?
Sajan Gautam: It was one thing led to another. So it was not a straight line. It was a very curvy path, because one thing led to another. I wanted to explore something and then cut into something else.
Betsy Peters: So, now that you’re 20 years in, tell us a little bit about the role.
So what does a Chief Information Security Officer at Arvest Bank do, and what are some of the most interesting aspects of your job?
Sajan Gautam: Yeah, sure. It’s a whole gamut of things, right? A whole wide spectrum of responsibilities. First, to think from security architecture, engineering, and operations. That includes, security operations include, threat intel collection, monitoring, incident response and the recovery side. So that is one area. Another is security program development and implementation, meaning identity and access management, vulnerability management, data security, all those, like insider threat and all those things. And then also thinking in terms of other areas such as security awareness.
So I’m also responsible for that. In addition to that, I’m also responsible for business continuity and business resiliency. So the overall business continuity and business resiliency, not just information security, business resiliency. Why is that? That is, that is because as a CISO, I do have the widest visibility in an organization, all the interconnectedness of the issues. So that’s why I’m also responsible for that. So a lot of the people who are used to thinking in terms of the NIST framework and all, I’m responsible for identification to protection. Detection, respond, and also the recovery of the things. So the whole gamut of things.
Betsy Peters: So that is a very wide scope. What areas are you the most passionate about?
Sajan Gautam: The passion changes when I do learn more. Because when, lately, for the last couple of years, I’ve been more passionate about data security. And how we can use emerging technology to secure the data. Because that is also accidental, too, because when we started looking into the security operations, uh, what type of data we’re collecting, where those data flow from one place to another, then it’s like, Oh, now I need to learn more about the data.
So one thing led to another there.
Betsy Peters: That’s great. Well, so I want to dig more into that. I think particularly in financial services, customer trust is so paramount. So. Is this fascination with the data connected with that creation of customer trust and a focus on cybersecurity? So tell me a little bit about, um, how you see your job impacting customer trust at the bank.
Sajan Gautam: Yes, absolutely. Right. So as a financial organization, uh, we tend to collect a lot of the data and for business purpose, for good reasons. Financial institution or banking is the business of data. We do make a lot of the business decisions based on the data. So trust is very paramount. So not just from the data perspective, banking as a business is a business of a trust.
So we need to establish trust with the customers. How do you do that? There are multiple avenues. First is being very transparent with What we collect and how we what we collect and how we use that. Are all the financial institution do it? Maybe. More or less, right? More or less, some do it, but that is the fascination that got me into this thing.
Betsy Peters: And do you have any rules of thumb that you give your staff about customer trust? And how their jobs interact with that at the brand level for the bank?
Sajan Gautam: Yes, absolutely. There are first is be open about what to collect and why to collect, right? Because if I’m a customer, I want to know why. The bank or the financial institution is collecting my data.
What is the relevance of that certain information? That is how we start. And then as much as possible, share how that data is going to be used. And in case there is a compromise, how we are going to be communicating with them. So that is the foundation of it.
Betsy Peters: We had a little bit of talk offline about over collecting data.
And I’d love to know how you think about that. And again, how you communicate that with your teams. It’s very easy these days to collect as much data as possible, but what kind of rules of thumb do you set down to make sure that people can trust you because you’re not over collecting?
Sajan Gautam: Yeah, absolutely. So, this is a shift in the thinking, and I learned this from a friend of mine. Friend, mentor, Sonny Leo, he is, I mean, we used to call, talk about data security and all these things, and then he flipped that, like, oh, there’s a proliferation of data everywhere. But if you think about data as a liability, instead of data as an asset, you collect only what you need.
Because when you think about asset, when you think about data as an asset, you over collect. You want to collect everything you want to accumulate assets. But when you think about data as a liability, you still collect them because we don’t collect liabilities for our mortgages for everything, right? But when you collect that as a lie, when you think that as a liability, you collect only what you need.
So that’s a mindset change. And I communicated that to our. Employees and associates as well. And we do have several cyber security awareness message centered around data as a liability. That’s a mindset change.
Betsy Peters: I think it’s a fascinating point. I’ve never heard anybody say it in that way, and I think it’s a really provocative, uh, way to think about it.
I guess my question, so as you know, our audience is primarily of revenue technology practitioners. CRM, marketing and sales operational type roles. What would your suggestion be about how they make that shift? What are some good examples of what thinking about data as a liability looks like in a bank?
Sajan Gautam: Yeah. First is like thinking about data as a liability. If we are, so there’s a multiple way that I can answer that question, right? First one is when we think data as a liability, we do not collect. Now we are saving the storage cost on it. If there is a data discovery situation for litigation and all those things, we are saving money there.
We are saving money on the retention and all those things. So that is a, that may not be a direct revenue generation that is saving on the cost. So that is one, one way to take a look at it. Another way is define the use cases. Before collecting the data, think how we are going to use that data. We have a habit of over collecting things without defining the use cases.
So define the use cases, one strong approach. Another is don’t collect what you don’t need.
Betsy Peters: Yeah, I think that’s really the use case. One in particular, I think, is making its rounds in the sales and marketing profession around. If you can’t action on it, why do you have it type of question? That I think resonates here and I think again goes along the lines of creating data trust with your customers because the more you collect and create a dragnet, the more nefarious uses or, you know, not even sometimes unintentional uses can happen and really create huge problems for brands.
And then, you know, getting into the next level around cyber security threats, how are you staying ahead of the curve when it comes to keeping this data about your customers secure and safe?
Sajan Gautam: Yes, um, this is what we say, learn from others and let others learn from you. So that is what I mean by that is we do participate in different type of forums.
From the information security professional as well as non information security professional that way we learn from each other. So that is like, that is one approach. Another very good avenue for our learning has been the startup community. I do love the startup community because these small startups solve the problem much quicker, much faster than these big behemoths.
Betsy Peters: So that has been another avenues for our learning and sharing information and are you doing these in person? Are these on discord? Like what? What are the typical mechanisms for sharing and learning for your all the above all the in person? Because there are in person, formal collaboration, informal collaboration.
Sajan Gautam: Talking about something else, and then something else pops up, we just pick up the phone and talk. And other times we just, sometimes we just grab drinks, and we talk about these things. So, all the above.
Betsy Peters: That’s great. Let’s talk a little bit about AI and machine learning. So what’s the most promising innovation that you’re actually using at the moment when applied to cybersecurity?
Sajan Gautam: Yeah, there are multiple. One is like, so this is how I do think about use of AI and ML in information security or in general. Machine learning or AI, they are better than human. On data analysis, that means wherever we are collecting the data or wherever we are using the data, there is a use for AI and ML.
So thinking about any use case where we are using the data, we are using a whole lot of data in compliance. That is area. We do use it. We do use a lot of the data in threat analysis are threat monitoring areas. A lot collection, incident management, those are all the areas where AI and ML can be used very efficiently because AI and ML can do it much quicker, much faster and more accurate than a human does.
Betsy Peters: So, yeah, I was going to say, can you give us some example of like the scale of improvement you’ve been able to put in place given some of these new innovations you’re testing out?
Sajan Gautam: Yeah, absolutely. Absolutely. Especially on the threat intel, you know, within the security operations center, uh, when we use the machine learning, uh, we can get the data much quicker.
80 percent improvement over there. Wow. Yes, 80 percent improvement. And then we can also use that to create the playbooks. So instead of human creating the playbooks, based on the patterns, the ML and AI would create the cybersecurity playbooks on its own. So that’s another area.
Betsy Peters: Yeah. So just so I’m sure I understand that, essentially, you’re asking the language model to tell you how it’s identified the risk and it writes it up for you.
Yeah, that’s great.
Sajan Gautam: Absolutely. So data dump in one area, right? And then, AI and ML, they look into the data patterns used and all, and then they do help us create the playbooks accordingly.
Betsy Peters: And so what do you do with an AI generated playbook? Do you play it back into the AI to continue to get more accuracy outing?
Sajan Gautam: Yes, it’s a, you call it like iterative learning. So it refines over time. And then when it fails to accurately predict, it will automatically, that… Process automatically goes down and it starts another loop.
Betsy Peters: That’s interesting. How did, how does this new type of workflow change the talent you need? Or change your team structure in any way?
Sajan Gautam: Yeah, it does a little bit because, uh, it does augment, the talent to look into the higher level of pattern matching. High level, higher level of decision making than doing this data collection and analysis by human eyes. So it is kind of elevating the work from an operator to the analyst level.
Betsy Peters: And, I assume that the perpetrators that are working against you trying to break into the bank or access the data, they’re using as sophisticated models as you are at this point, right? So it’s almost like you have to fight fire with fire in that regard.
Sajan Gautam: Absolutely. Absolutely.
Betsy Peters: Interesting. Tell me what’s a good example that you could share, like a use case of something that, other than this 80 percent improvement, which is phenomenal, but is there something that the average person who banks might be able to say, wow, that’s amazing and thank you, because you’re protecting me in a way I didn’t even know?
Sajan Gautam: I mean, one other areas that bank or financial institution can look at, AI, ML is on the fraud detection, right? Sure. Fraud is another area. Where we collect a whole lot of data and that is where the pattern matching and all those comes in if one integrates the threat Intel and then the internal analysis or internal data and do some kind of Algorithmic work there.
I think there’s a big opportunity there.
Betsy Peters: Sure. So early detection. Someone who stole your credit card, for example, and is using it at a gas station and that kind of thing
Sajan Gautam: Yes, and also areas in the AML, Anti Money Laundering Area. That is also Bank Secrecy Act, BSA. That is another area. So there’s so much opportunity there.
Betsy Peters: That’s great. Let’s switch to another aspect of your job. What role does the CISO play when it comes to compliance in banking? And how is AI and ML being deployed to assist with regulations?
Sajan Gautam: Yeah, I mean, CISO plays a pretty significant role there because if you think about compliance, compliance sets the rule, but the implementation, that more or less falls into the CISO’s area, right?
Betsy Peters: The privacy… So the adherence to the regulation, yeah.
Sajan Gautam: Yeah. So… If there is a regulation there, how do we actually operationalize it within the bank or within any organization? CISO is involved in those. So, there may be regulatory compliance, then how do we enforce that? CISO plays the role in that. So security operations, that is where we work hand in hand with the compliance, privacy, BSA.
Team fraud, all the above.
Betsy Peters: And is there, is this an area where you’re working with your RevOps team more so in terms of making sure the things that are stored in CRM, the material non public information, for example, isn’t shown to people who shouldn’t be seeing it? How involved do you get with your RevOps teams when it comes to compliance and data capture and data display?
Sajan Gautam: A whole lot because, yeah, a whole lot. Because We tend to collect. I mean, it’s a human nature, right? We tend to collect more information, even when we don’t need it. We all have our grandmas, myself included, my moms, and everybody collects the data, right? Everybody collects. We are, we are data hard. So that is one area that we work with.
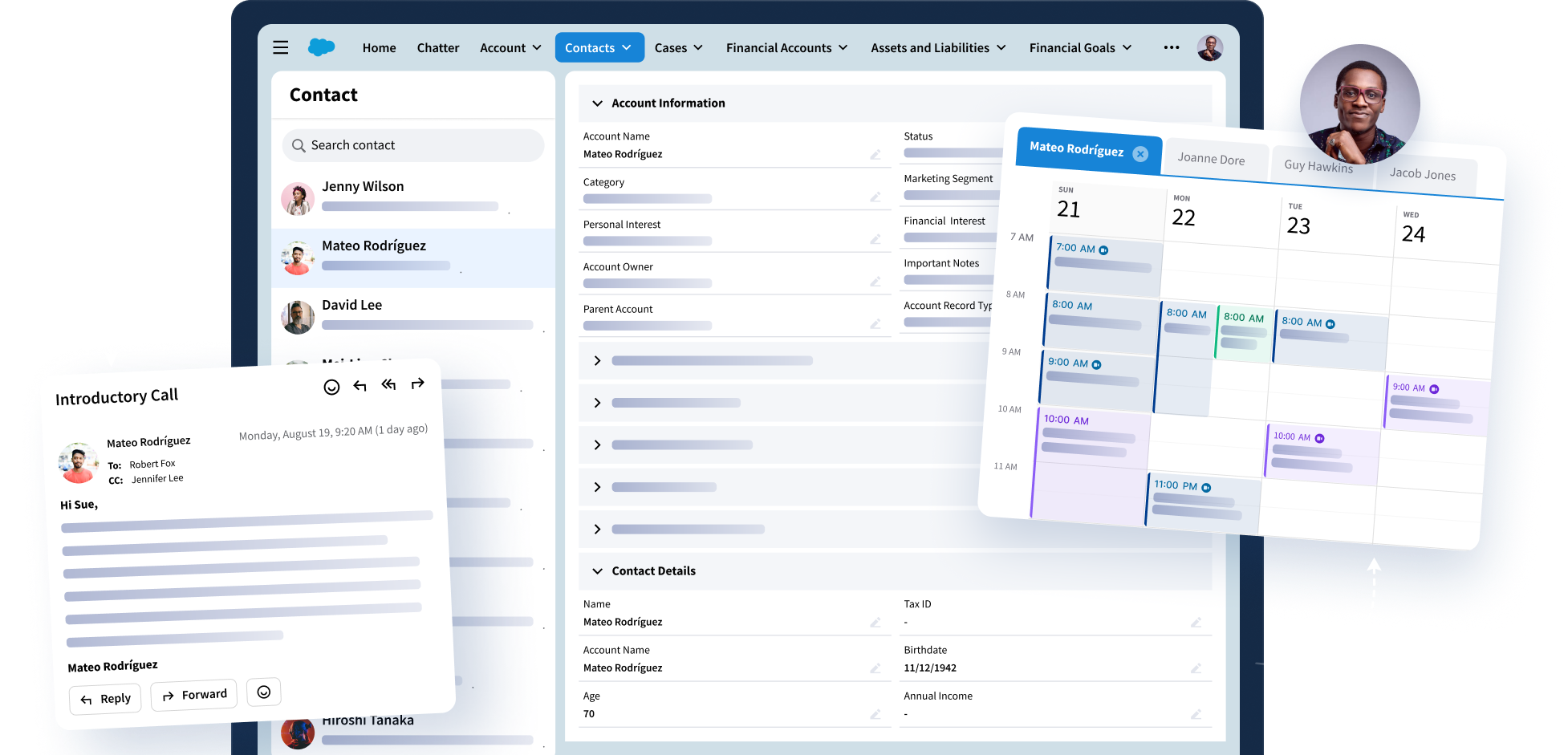
And also, we think about, like, We are collecting the data, but are we putting that in the right place? Are we putting that in a flat file versus are we putting that in a secure, structured database such as CRM?
That is where we do talk with the Revenue team quite a bit.
Betsy Peters: Sure, and even around permissions, I imagine your early work in that and being interested in that, I’m sure, plays a part.
Sajan Gautam: Yes, absolutely. Because it’s such a large organization. Yeah, we have to secure the data during the collection process itself.
If we do not secure the data during the collection process and we think like, oh, we’re going to collect the data and then secure afterwards, that will never happen. Deal with it later. You know, right? That will never happen. So that is where the value of CRM comes into play.
Betsy Peters: Absolutely. Have you ever been called upon to have a difficult conversation about policies and breaches?
And if so, how do you approach those sticky conversations?
Sajan Gautam: So that is usually, that is where the education comes in, right? The education, not just for the employee or the associate education, the education to the executives. So, periodic education. So, what, what are those education look like? Letting them participate in various activities.
So, for example, this month is Cybersecurity Awareness Month. We let the executive craft their message and talk to our associates or employees about cybersecurity awareness without me getting involved. So that way, they are stakeholders. So all the executives are stakeholders in cybersecurity. So that is one avenue.
Another is getting them interested through different kind of tabletop exercise with plausible scenarios. Let’s take some of the examples from, like widespread reach. And then we play that as a scenario in our tabletop exercise. And we let them come with the decisions and all. In a safe environment.
That’s when it becomes a learning environment. So that is second approach. And the third is be very open about the challenges. Do not sell them on the fear, but also do not over promise them. Because sometimes we tend to tilt on either side. Sometimes we just like, we sell it too much on the fear, and the other time we over promise them.
Don’t do that. So. When we do that, we establish the trust with the executives, and then they do support the program.
Betsy Peters: What are a few tips that you have on how to strike that balance? I think, I think your point is dead on, but that’s tricky to do, right? So what’s your internal compass on that? How do you navigate those waters?
Sajan Gautam: It’s a lot, many times it’s a hit and trial, practice it over time, because establishing trust takes time. Breaking trust does not. Establishing trust takes time. So. Yeah. Education in a safe environment, learning environment. So if we are, let’s take an example of tabletop exercise, cyber tabletop exercise.
Instead of giving them a very tough assignment on the first go, give them a very easy assignment just to get their muscle memory kick in. They start practicing it and then you gradually start making it harder. That’s how you establish the trust. That’s true with anything, right?
Betsy Peters: Sajan, we’d love the chance to peer into your crystal ball. So, looking ahead, what trends or developments do you foresee in this landscape that you specialize in, especially concerning AI, ML, the new developments on the horizon that are changing the game for everyone?
Sajan Gautam: Yes, I just see too many areas where AI and ML will be used extensively, and both of those are the areas of intensive data.
So wherever we are, uh, using more data, that is play room for AI and ML. So that means, in data analysis, customer data collection. Creating the customer relationship management based on the customer behavior and all those things. So that is one area where I do see a lot of potential for AI and ML.
Another is to support that security operations. Because when the business goes into data collection, data analysis and all, security has to Play a part in securing those data. That is where I do see more use of AI and ML in the security operations. So those are the two main areas that I do see.
Betsy Peters: How about prediction?
So prediction around fraud and all of that. Is that inside of the two areas you’re talking about? Or is that a different frontier from your perspective?
Sajan Gautam: I would put that within those two buckets. But we can spell that out separately. But fraud, AML. Secrecy act compliance on all those fit into either in the back end office, like security operations or the front end into the CRM area.
Betsy Peters: And as you’re looking at particularly on the predictive side, as you’re getting into the algorithms. Are, are you guys, how do you think about auditing the algorithms and making sure that, you know, you don’t make a bad call about someone, for example? Because we know data sets could be flawed and all of the things that we know about.
Sajan Gautam: I don’t think anybody has cracked that yet. That is still in development, but it only starts with the transparency, right? Because, my motor is. Do not use an algorithm that you do not understand, right? Do not go into a black box, thinking like, Oh, we did just collect the data. And then this proprietary EIML model will do its magic.
And then something comes poof. No, that doesn’t work that way. Because if you do not understand it, don’t use it. If you cannot explain it, don’t use it. We do still have to do a lot of homework there as a community there.
Betsy Peters: Yeah, and I think it’s interesting, like, your, your passion around learning, it sounds like, puts you in good stead here because, of course, you can think you understand everything.
And then, of course, you learn about edge cases that you have to kind of bring back in. I bring this up because, for example, my son was out of his geographic area where he normally uses his credit card and everything got shut down and he was being a good actor but didn’t call in and of course fraud detection would pick that up.
But it was his first time ever as a credit, you know, new credit card holder learning that. And you know, just interesting to know what data points that we can be pulling in. To be better at that, and where are the acceptable ranges of mistake, like that one was, obviously, because he just had to make a phone call to get it turned back on.
So I think this kind of constant learning about what the data is telling us and what the algorithms are really surfacing for us in terms of human activity or bias or whatever the case may be, is just a fascinating frontier, like you said.
Sajan Gautam: Yeah, absolutely. Absolutely. As machine is learning, we as human, we are also learning, right?
We are learning about the machine and we are learning about ourselves too. That’s it.
Betsy Peters: It’s almost like a big mirror back to us, isn’t it?
Sajan Gautam: Yeah, absolutely. Absolutely.
Betsy Peters: Yeah. So, to close up, Sajan, you said you have a lot of resources that you use and it sounds like you have a really robust network of people that you rely on to keep yourself sharp.
Are there any places that you would recommend a revenue operations or revenue technology specialist? should go to get up to speed on your world and the things that they might do to help you.
Sajan Gautam: Yeah, absolutely. There are, I mean, I, I cannot recommend FSISAC, Financial Services, Information Security, and Coordinating Council enough because that is an industry focus.
So if somebody is trying to generate the revenue through financial services, providing services to the financial services, that may be one. Industry particles, industry events, once we attend, that way one can learn what’s happening in the financial industries as well as they get to talk to the cyber security professionals and all, and who knows, we do need people from different fields, maybe working in the cyber security for some time.
Betsy Peters: That’s really interesting.
Is there anywhere that beyond the four walls of your institution where they could learn about this concept of data as a liability? Like, I think that’s really a fascinating, like you said, mindset shift. Is there any group of people who talk that way that they could tap into? Or a book? Or podcast?
Or do you just need to write a book?
Sajan Gautam: There are several. I mean, I cannot think of anything on top of my head right now. But if I do remember, I’ll just send that to you.
Betsy Peters: Yeah, that’s great. And maybe what we’ll do is we’ll Google it and see what we can find, because I think that’s a really fascinating concept that, um, good provocation for us to all talk about.
Sajan Gautam: Yeah, absolutely. Yeah, if I do remember, if I do find out, I’ll send that to you. Wonderful.
Betsy Peters: Anything else you’d like to leave the audience with?
Sajan Gautam: I think we covered quite a bit, like a wide range of topics. Uh, we did rhetoric.
Betsy Peters: Nothing jumps up. Very fun to talk to you. Thank you so much, Sajan. Thanks for your time today and your interest in talking to us.
Sajan Gautam: Yeah, sure. Thank you. Thank you for the opportunity. I really enjoyed this conversation.