Data Trust Suffers When Your Communications and Revenue Stacks Don’t Talk to Each Other
Shopping for a new (or improved) way to connect the systems that support your Go-to-Market teams is no small task. Because the choice drives the connection between—and access to—the CRM of data lake housing customer and deal data, the decision will profoundly impact how the organization operates. Matters of data governance, completeness, and quality inform the trust your organization has in its data—for better or worse. At the end of the day, your choice will affect the use of and trust in the data they use to build customer relationships and close sales.
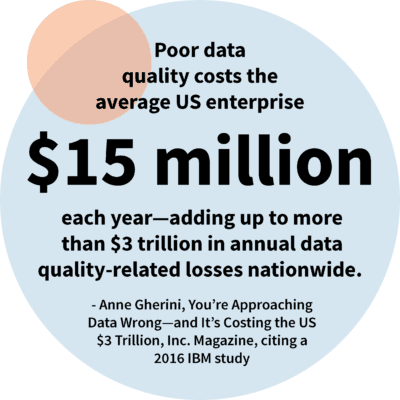
Poor data quality costs the average US enterprise $15 million each year—adding up to more than $3 trillion in annual data quality-related losses nationwide
In this first installment of a two-part post, we’ve compiled a list of five primary data trust challenges to keep in mind when shopping for the right revenue data solution.
Top 5 data trust challenges
1. Your platforms don’t talk to each other, and you are relying on end-users for data entry
CRM, email, chat, and other communications applications do what they do well—and they continue to improve. But, you have a critical gap to address. Why? Because the data in these platform-specific silos don’t automatically connect. As a result, users who live in CRM have access to revenue data gathered via CRM—and users who live in Outlook/Exchange and Google Workspace have access to data collected via those platforms. While some enterprises mandate manual data migration from one platform to the other, that approach is a risky half-step prone to errors, omissions, and duplication—resulting in low-quality data users can’t trust. We’ll go deeper into those issues below.
2. Your end-users are not particularly good at data entry—and it takes them away from customers
In addition to the data quality and completeness issues associated with manual transcribing customer data from CRM to other communications platforms—and vice versa—the practice is woefully inefficient. In an enterprise environment, even the most minor inefficiencies are compounded by the volume of each user’s customer interactions, multiplied by the sheer number of users routinely performing manual entry tasks. When 500 users interact with 20 customers daily, as few as 12 minutes of redundant data entry adds up to more than 500 wasted hours each week—time better spent in conversation with customers, building relationships, and building the path toward greater customer lifetime value.
3. Your users’ data entry mistakes are compounded when other users rely on data that are omitted, incomplete, and/or inaccurately transcribed
When one end-user omits critical data gleaned during a customer conversation—or makes errors in their efforts to transcribe that data from one platform to another, subsequent engagements with (or regarding) the same customer are compromised and compounded over time. Because that customer’s history is then incomplete—and possibly erroneous—later end-users who rely on that data can’t make fully-informed recommendations or pick up customer interactions where they left off. Often, this means customers must provide the same information again or correct ill-informed assumptions.Today’s customers bring high expectations to interactions with vendors—and even minor errors or inconveniences can diminish their trust in a vendor’s knowledge, commitment, and ability to deliver. Throughout multiple interactions, the risk of additional errors increases, potentially increasing customer history inaccuracy and confirming their sense that your enterprise lacks the sophistication necessary to answer their needs effectively.
4. End-users may gain access to customer data they’re not authorized to see—putting the data at risk of misuse or breach and elevating the threat of compliance violations
For enterprises in regulated industries, customer data security and compliance are essential. Once gathered, these enterprises bear full responsibility to secure sensitive revenue data and observe strict regulations governing its use. Data must flow to the right screen for the right user to prevent breach or misuse and must be consistent in all the applications they use.It’s essential to maintain consistent protocols that limit access to authorized users—strictly for authorized uses. This complex challenge is further complicated when customer data is housed in the individual data silos of a growing number of rev and comm platforms, requiring duplicative security and compliance protocols that complicate monitoring and enforcement—and, in some cases, may expose sensitive data to increased risk of breach.
5. Disconnected platforms inhibit efforts at data governance—potentially exposing sensitive data to the risk of unauthorized use
Because building data trust across an enterprise is an ongoing obligation, the ability to audit end-user behaviors and configure (and reconfigure) key processes and related data flows is essential. Absent comprehensive governance of data flows, it’s difficult for administrators and managers to control the distribution of sensitive data—including material non-public information (MNPI). This shortcoming prevents visibility into which users have access to sensitive data—and how they’re using it—making it difficult to nip potential misuse in the bud and mitigate security and compliance risks. As with the challenges discussed above, these processes are complicated when revenue data is siloed in multiple communications platforms, resulting in decreased oversight, increased risk of compromised data quality—and undermined data trust.
Conclusion
 Knowing the challenges, you’re likely to face as you begin to create your requirements gives you a head start. And while your enterprise may not suffer from the issues we’ve highlighted here, the list provides a helpful starting point to assess your firm’s unique situation. Once you have a clear sense of the data trust challenges on your horizon, you’ll be in a much better position to seek the best, most impactful revenue data ops solution.
Knowing the challenges, you’re likely to face as you begin to create your requirements gives you a head start. And while your enterprise may not suffer from the issues we’ve highlighted here, the list provides a helpful starting point to assess your firm’s unique situation. Once you have a clear sense of the data trust challenges on your horizon, you’ll be in a much better position to seek the best, most impactful revenue data ops solution.
To make that task more manageable, we encourage you to read the second installment of this post, 5 Data Trust Solutions to Reduce Risk of Bad Revenue Data – Part II, where we’ll detail the recommended solutions.
Latest Articles
- Guide to Einstein Activity Capture: All You Need to Know
- 2024 Bankers Summit: 5 Key Takeaways
- Financial Services: Mastering Customer 360 and Client Engagement for Increased Customer Lifetime Value
- Dreaming Big at Salesforce Education Summit San Diego 2024
- How to Build a Sales Cadence in 2024: Examples and Best Practices

